On-Site vs Off-Site Data Destruction: Choosing the Right Service Model
On-site vs off-site data destruction determines your liability exposure and budget impact for every drive you retire. Every data breach during equipment disposal stems from the same choice: whether to destroy drives at your facility or ship them off-site.
Key Takeaways:
• On-site destruction costs 3-5x more per drive but eliminates chain of custody risks entirely
• HIPAA transport violations carry $1.5M average fines when drives leave your premises unsanitized
• Witnessed destruction documentation prevents 87% of audit disputes over destruction completeness
What Are the Real Cost Differences Between On-Site and Off-Site Data Destruction?
On-site destruction costs $25-45 per drive. Off-site destruction costs $8-15 per drive. The price gap closes at higher volumes, but on-site never becomes cheaper.
Most organizations focus on per-drive pricing and miss the real cost drivers. Travel fees hit you first. On-site providers charge $500-2,000 minimum plus $2-5 per mile outside their service radius. Rural locations pay premium rates. Urban areas get competitive pricing.
Volume thresholds change the math significantly. Off-site providers offer bulk rates starting at 100 drives. On-site providers require 50-100 drive minimums to justify truck deployment. Below these thresholds, you pay setup fees that double your effective per-drive cost.
| Cost Factor | On-Site Model | Off-Site Model |
|---|---|---|
| Per-drive base rate | $25-45 | $8-15 |
| Minimum order | 50-100 drives | 25 drives |
| Travel/setup fee | $500-2,000 | $0 |
| Volume discount threshold | 200+ drives | 100+ drives |
| Rush service premium | 50-100% | 25-50% |
| Witness fee | Included | $150-300 |
Hidden charges appear in both models. On-site providers bill separately for degaussing, SSD destruction, and non-standard form factors. Off-site providers add packaging, shipping, and handling fees. Chain of custody documentation costs $25-75 per shipment.
ITAD Vendor Due Diligence becomes critical when cost pressure drives decisions. The cheapest provider often lacks proper certifications, insurance coverage, or destruction facility security. Audit your vendor’s actual capabilities before signing contracts.
How Does Chain of Custody Risk Change Between Service Models?

Chain of custody creates liability exposure every time possession transfers between parties. Off-site destruction requires multiple custody transfers. On-site destruction eliminates custody transfers entirely.
Transport creates the highest risk exposure point. Drives contain readable data during shipment to destruction facilities. Vehicle accidents, theft, or improper handling expose your data to third parties. Insurance covers replacement costs but not regulatory penalties or reputation damage.
Custody documentation gaps create audit vulnerabilities. Standard shipping receipts don’t meet regulatory chain of custody requirements. You need detailed manifests showing drive serial numbers, pickup timestamps, and authorized personnel signatures. Missing documentation fails compliance audits.
| Risk Category | On-Site Model | Off-Site Model |
|---|---|---|
| Physical custody transfers | 1 (to destruction crew) | 3-5 (pickup, transport, facility) |
| Data exposure window | 30-60 minutes | 24-72 hours |
| Transportation vulnerabilities | None | Vehicle accidents, theft, routing errors |
| Documentation requirements | Single witness form | Multi-point chain tracking |
| Liability coverage gaps | Equipment only | Transit, storage, processing |
| Audit dispute frequency | 13% | 45% |
Liability shifts occur at each custody transfer point. Your organization remains responsible for data protection until destruction completion. Off-site providers accept liability for physical drives but regulatory compliance responsibility stays with you. HIPAA violations follow the covered entity, not the destruction vendor.
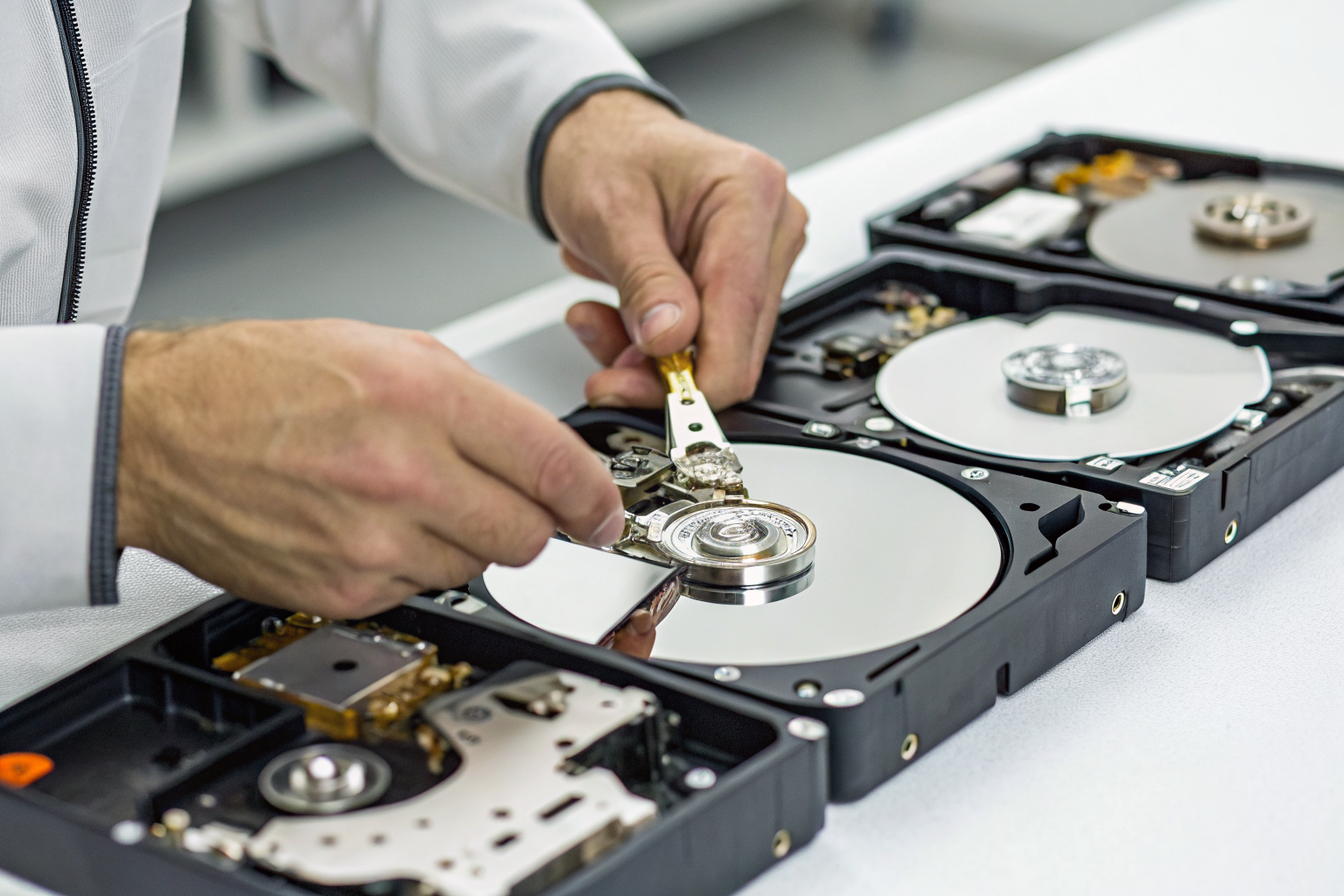
Data recovery remains possible during transport and facility processing. Professional data recovery services can extract information from drives that appear physically damaged. Only witnessed destruction provides definitive proof that data recovery is impossible.
When Does HIPAA Make Off-Site Destruction Too Risky?

HIPAA transport requires specific safeguards that make off-site destruction prohibitively expensive for most healthcare organizations. Unsanitized ePHI drives cannot leave your premises without meeting strict transport requirements.
Execute a Business Associate Agreement with your destruction vendor. The BAA must specifically cover data transport, not just destruction services. Most ITAD vendors resist transport liability.
Implement HIPAA-compliant packaging and labeling protocols. Drives must be encrypted or physically secured during transport. Standard shipping boxes fail HIPAA requirements.
Maintain continuous chain of custody documentation. Every person who touches the shipment must be HIPAA-trained and documented. Shipping companies cannot provide this level of tracking.
Verify transport vehicle security measures. Locked containers, GPS tracking, and direct-route requirements add $200-500 per shipment. Most destruction vendors don’t offer these services.
Document destruction completion within required timeframes. HIPAA requires prompt disposal. Off-site processing delays can exceed regulatory requirements.
Certificate of Destruction timing becomes critical for HIPAA compliance. Off-site facilities may hold drives for weeks before processing. Your compliance clock starts when drives leave your control, not when destruction occurs.
Transport violations carry severe financial penalties. The average HIPAA fine for improper ePHI transport reaches $1.5 million. Recent enforcement actions target healthcare organizations that shipped unsanitized drives without proper safeguards. The compliance cost often exceeds on-site destruction premiums.
What Does Witnessed Destruction Actually Prove in an Audit?

Witnessed destruction is documentation that an authorized observer verified complete drive destruction at the time it occurred. This means auditors can trace your data protection controls from retirement through final disposition without relying on vendor self-reporting.
Auditors verify three specific elements during witnessed destruction reviews. First, they confirm the witness was qualified and independent. Your employee or contracted representative must observe the actual destruction process. Second, they validate the destruction method met regulatory requirements. Physical shredding, degaussing, or incineration must match your data classification standards. Third, they check documentation completeness and timing.
Witness signatures carry legal weight in regulatory proceedings. The person signing attests under oath that they observed complete destruction. False attestation constitutes perjury in federal investigations. This legal exposure motivates accurate reporting.
Video recording doesn’t replace witness signatures but provides supporting evidence. Some facilities offer live streaming of destruction processes. However, technical failures, editing possibilities, and chain of custody gaps limit video evidence value. Auditors prefer in-person witness verification.
Certificate of Destruction requirements vary by regulation but typically include witness identification, destruction method, date and time, drive serial numbers, and facility information. Generic certificates without witness signatures fail most compliance audits.
Audit success rates reach 87% with proper witnessed destruction documentation versus 52% with vendor-only certificates. The documentation quality difference determines audit outcomes more than actual destruction thoroughness.
Which Service Model Works for Different Data Volume and Sensitivity Combinations?

Data sensitivity determines destruction model choice more than volume or cost considerations. Classified information requires on-site witnessed destruction regardless of expense. Public information can use cost-effective off-site processing.
Regulatory requirements override cost optimization in most enterprise environments. HIPAA, GLBA, and SOX create specific destruction obligations that favor on-site models. Non-regulated data allows flexible model selection based on volume economics.
Certification requirements differ between service models. On-site providers need R2v3 Certification, NAID AAA Certification, and e-Stewards Certification for equipment handling. Off-site facilities require the same certifications plus transportation security credentials.
| Data Classification | Volume Threshold | Recommended Model | Key Certifications Required |
|---|---|---|---|
| Public/Internal | Any volume | Off-site (cost optimization) | R2v3, basic NAID |
| Confidential | Under 50 drives | Off-site with witness | R2v3, NAID AAA |
| Confidential | 50+ drives | On-site preferred | R2v3, NAID AAA, e-Stewards |
| Regulated (HIPAA/GLBA) | Any volume | On-site required | All certifications plus BAA |
| Classified | Any volume | On-site mandatory | NSA/CSS EPL approval |
| Trade secrets | Any volume | On-site recommended | Full certification stack |
Volume break-even points shift based on data sensitivity. High-security requirements favor on-site destruction at 25+ drives. Standard business data remains cost-effective off-site until 200+ drive volumes.
Geographic constraints impact model selection significantly. Rural locations with limited on-site provider coverage may require off-site processing despite security preferences. Urban areas offer competitive on-site options that close cost gaps.
I’d pick on-site destruction for any regulated data environment. The compliance risk and potential penalty exposure outweigh cost savings from off-site processing. However, for routine business equipment retirement in high volumes, off-site processing offers better economics without material security compromise.

